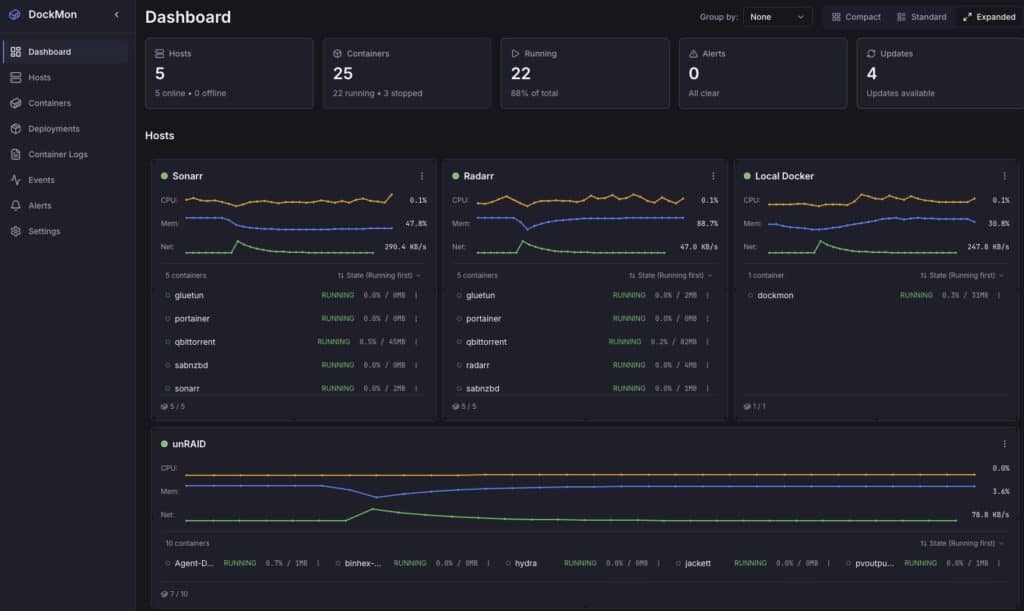
Yes: DockMon exists, and it looks great for developers and IT teams who live in “plain Docker.” It’s a free and open-source project that delivers real-time monitoring, intelligent container auto-restart, multi-channel alerts (Discord, Slack, Telegram, Pushover, Gotify, SMTP) with customizable templates, multi-host from a single pane of glass, and a security-by-design posture (mTLS for remote hosts, rate limiting, Alpine base). All of this without spinning up a full Kubernetes cluster or a Prometheus+Grafana+Alertmanager stack.
In short, it targets the “most teams’ needs” for operating Docker with observability and reaction: see metrics, logs, events and—crucially—take action (restarts, deployments, bulk ops, health checks, maintenance windows, scheduled image updates).
What it brings
- True multi-host: inventory of local and remote Docker hosts with optional mTLS to harden the link.
- Real time: per-container CPU, RAM, and network, with WebSocket updates and drag-and-drop dashboard widgets.
- Live logs: simultaneous viewer for multiple containers with follow and filters.
- Event viewer: full audit trail, search, live updates.
- Intelligent auto-restart: per-container with configurable retry logic (avoids loops and thrash).
- Multi-channel alerts: Discord, Slack, Telegram, Pushover, Gotify, SMTP; templates and rules per condition (CPU, memory, health-check failure, restart storm, etc.).
- Deployments & bulk ops: run/compose, reusable templates, start/stop/restart at scale with progress tracking.
- Auto-updates: detect and schedule image updates.
- HTTP/HTTPS health checks: with auto-restart on failure.
- Blackout windows: silence alerts during maintenance.
- Modern stack: backend FastAPI (Python 3.13) + Go metrics service, frontend React 18 + TS, Nginx reverse proxy, Alpine base.
v1→v2 migration: preserves hosts, containers, history, and users; you must recreate alert rules, regenerate mTLS certs due to OpenSSL 3.x requirements, and a one-time schema migration runs automatically from v1.1.3 to v2.0.0.
Who it’s for
- Teams without Kubernetes (for simplicity, cost, or size) who want monitoring + reaction without standing up half the cloud.
- Homelabs and SMBs who value alerting and basic auto-remediation (restart, update) without losing control.
- DevOps/SRE that need a lightweight multi-host solution for edge nodes, CI runners, or remote hosts.
Quick comparison with familiar alternatives
| Criterion / Tool | DockMon | Portainer CE | Dozzle | Watchtower | Prometheus + cAdvisor + Alertmanager + Grafana |
|---|---|---|---|---|---|
| Scope | Multi-host, metrics, logs, events, actions | Docker/K8s UI mgmt, stacks, RBAC | Log viewer | Image auto-update | Rich metrics/alerts (piecemeal stack) |
| Real-time metrics | Yes (per-container CPU/RAM/net) | Basic/limited | No | No | Yes (very complete) |
| Built-in alerts | Yes (Discord/Slack/Telegram/SMTP, templates) | No native | No | No | Yes (Alertmanager; config required) |
| Smart auto-restart | Yes (retries) | Docker policy (simple) | No | No | No (orchestrate elsewhere) |
| Auto-updates | Yes (scheduled) | Partial (edition/flows dependent) | No | Yes (main focus) | No (external tooling) |
| Compose/run deploys | Yes (templates & multi-host) | Yes | No | No | No |
| Multi-host | Yes (optional mTLS) | Yes (multiple endpoints) | No | No | Yes (federation; higher complexity) |
| Learning curve | Low-medium | Low | Very low | Very low | High (many components) |
Takeaway: DockMon won’t replace Portainer if you need full Docker/K8s administration, but it covers observability + reaction with fewer moving parts than Prometheus+Grafana and more reach than Dozzle/Watchtower on their own.
Quick start (compose in 5 minutes)
# docker-compose.yml
services:
dockmon:
image: ghcr.io/darthnorse/dockmon:latest
container_name: dockmon
restart: unless-stopped
ports:
- "8080:8080" # UI
- "8443:8443" # API/WS if you split ports
environment:
DOCKMON_ADMIN_USER: "admin"
DOCKMON_ADMIN_PASS: "change_this"
DOCKMON_TIMEZONE: "Europe/Madrid"
# Notifications (examples; optional)
DOCKMON_SMTP_HOST: "smtp.your-domain.com"
DOCKMON_SMTP_USER: "[email protected]"
DOCKMON_SMTP_PASS: "secret"
DOCKMON_TELEGRAM_TOKEN: "12345:bot_token"
DOCKMON_TELEGRAM_CHAT: "-100123456789"
volumes:
- dockmon-data:/var/lib/dockmon
- /var/run/docker.sock:/var/run/docker.sock:ro
volumes:
dockmon-data:
Code language: PHP (php)docker compose up -d- Open
http://your-host:8080and log in. - Add remote hosts if needed (see below).
Monitor remote hosts with mTLS (basic flow)
- Enable Docker API over TLS on the remote host (example daemon.json):
{
"hosts": ["unix:///var/run/docker.sock","tcp://0.0.0.0:2376"],
"tlscacert": "/etc/docker/tls/ca.pem",
"tlscert": "/etc/docker/tls/server-cert.pem",
"tlskey": "/etc/docker/tls/server-key.pem",
"tlsverify": true
}
Code language: JSON / JSON with Comments (json)- Open
2376/tcpin the remote firewall for the DockMon server’s source IP. - In DockMon → Hosts → Add host, set
tcp://IP:2376and upload client certificates issued by your CA. - Verify metrics and logs stream live.
Tip: for WAN nodes, use WireGuard or at least enforce mTLS, strict IP allow-lists, rate limiting, and auditing.
A typical alert rule
- Condition: container
webwith CPU > 85% for 3 min. - Action: send to Telegram + email and record incident in the event viewer.
- Remediation (optional): restart if > 95% for 5 min or if health-check fails.
The new v2 rule engine supports templates per channel and maintenance windows to silence during deploys.
Best practices (day-to-day)
- Avoid restart loops: use backoff, delays, and max retries per container; if exceeded, fire an alert rather than hammering restart.
- Labels & tagging: leverage Docker labels to categorize services, environments, owners; DockMon can derive tags automatically.
- Sane auto-updates: schedule off-hours, validate image digest, and enable blackout windows to suppress noise while updating.
- Security: short-lived sessions, TLS on the UI if exposed, and mTLS for remote hosts.
Limitations & edges
- It’s not an orchestrator: if you need auto-scaling, service mesh, or canary/blue-green deploys, you’re in Kubernetes or similar territory.
- Business-level alerting (SLOs, burn rate) will require your SIEM/observability platform or extending via API.
- For low-level observability (eBPF, tracing, profiling), pair it with specialized tools and let DockMon handle the operational side (alert + action).
Quick FAQ
Does it use many resources?
It’s lean for what it does, but real-time metrics and live logs across many containers/hosts add up. Size CPU/RAM and network for your fleet.
Can I integrate with Grafana or a SIEM?
Yes—exposes REST/WS APIs and events; use it as the operational source (incidents, restarts, health checks) and correlate in your platform.
Does it support compose and repeatable deploys?
Yes. You can store templates and launch deploys to remote hosts from the UI.
How do I migrate v1 → v2?
Core data migrates automatically; recreate alert rules, regenerate mTLS, and verify host connections post-upgrade.
Conclusion
For the vast majority who don’t need Kubernetes, DockMon bundles into a single box what’s often spread across several tools: see, alert, and act on containers in real time, across one or many hosts, and with sane security. It doesn’t aim to out-manage Portainer or out-instrument Prometheus; it complements those pieces—or replaces them when what you want is to operate Docker with clarity and quick reactions.
If your team lives in Docker and wants less fuss while staying informed and protected, it’s well worth a try.