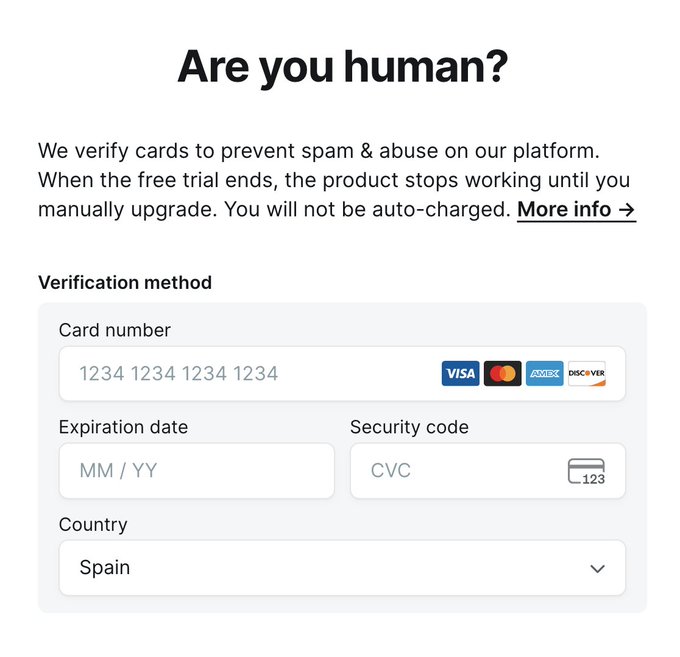
The pattern is showing up everywhere: you click Free trial, and the next screen asks for a valid credit card “just to verify you’re human,” often with a reassuring line like “you won’t be charged” and a Stripe badge for credibility.
For developers and sysadmins, this isn’t a UX gimmick. It’s a strategic shift: the goal isn’t to prove humanity, it’s to price out abuse. That has real consequences for security, fraud exposure, conversion, support load, and compliance.
It’s not a CAPTCHA — it’s an anti-abuse toll booth
CAPTCHAs try to separate humans from bots using interaction or perception tests. Card verification works differently: it assumes large-scale abuse requires something scarce (a payment method), so mass account creation is no longer free.
For products with high variable cost (LLM/GPU usage, API credits, scraping, media processing, bulk automation), free trials are a prime abuse vector: create account → burn credits → rotate → repeat. A card wall makes that loop more expensive, harder to automate, and more attributable.
But be precise: it doesn’t prove the user is human. It proves access to a payment instrument.
“Stripe makes it safe”… only if it’s integrated correctly
Stripe can reduce risk compared to homegrown payment forms, especially when implemented using Stripe Checkout or Stripe Elements:
- Card details are entered into Stripe components.
- The platform typically receives a token / PaymentMethod (not raw PAN).
- SCA / 3D Secure may apply in regions like the EU.
That’s materially safer — but it doesn’t eliminate all risk:
- Many flows perform a $0 or small authorization (sometimes $1) that can trigger support tickets or user anxiety.
- “We won’t charge you” can still mean “we might later” depending on terms, renewal settings, or user misunderstanding.
- Poorly designed flows can become a target for card testing (attackers validating stolen cards), leading to chargebacks and processor scrutiny.
Bottom line: Stripe isn’t magic. Safety depends on how you implement the flow and the controls wrapped around it.
What it actually mitigates (and what it doesn’t)
What it helps with
- Raises cost per account (even with virtual/prepaid cards).
- Reduces attack throughput (more steps, more failure points).
- Improves attribution (payment instrument signals, anti-fraud scoring, repeat patterns).
What it does not solve
- It’s not a reliable humanity proof. Bots can use stolen cards, synthetic identities, or purchased payment methods.
- It can increase your fraud surface (card testing, chargebacks).
- It won’t stop determined actors. It mostly kills cheap, high-volume abuse.
Operational impact: conversion, support, and reputation
A card wall is often justified by unit economics — but it affects ops immediately:
- Lower conversion: many users bounce when asked for a card, especially in low-trust or B2C funnels.
- Support load: “Will I be charged?”, “Why is there a pending authorization?”, “How do I remove my card?”
- Reputation risk: in social media, nuance disappears — “They ask for a card to try it” spreads fast.
This is always a trade-off between abuse cost and friction cost.
Recommended approach: use it as a layer, not the only defense
For security and platform teams, card verification can be effective — but it works best as part of a layered, risk-based strategy.
1) Cheap pre-controls
- Rate limiting by IP/ASN/region.
- WAF + bot management (automation detection, fingerprints).
- Device/session limits, cookie persistence.
- Email verification + heuristics (disposable domains, velocity, reputation).
2) Adaptive friction (risk-based)
- Require a card only when risk is high or when users request expensive capabilities (GPU mode, API access, bulk exports, high-resolution generation).
- Escalate friction based on signals (abnormal click speed, repeated endpoint patterns, multi-account behavior).
3) Real payment fraud controls
- Stripe Radar (or equivalent) with rules that specifically target card testing.
- Velocity controls: attempts per IP, per BIN, per fingerprint.
- Lock down patterns associated with carding: many declines, tiny authorizations, many cards per account, repeated CVV failures.
- Alerting into SIEM for anomalies in the verification funnel.
Is it “the solution” to bots and AI agents?
No. It’s an economic control that prices out low-effort abuse. It’s very effective against cheap bot waves and free-trial farming. It’s less effective against organized fraud — and it doesn’t “defeat AI.” It just makes large-scale automated access harder and more expensive.
The real lesson for 2026 is that anti-abuse has shifted: puzzles alone aren’t enough. Modern systems need signals, adaptive friction, fraud controls, and clear user messaging.
FAQ
Is entering a card for a free trial “safe” if it’s Stripe?
Often safer if the card entry happens via Stripe Checkout/Elements (tokenization), but risk still depends on the vendor’s terms, renewal behavior, and whether authorizations are used.
Does this actually prove the user is human?
No. It proves access to a payment method. It blocks cheap bots, not determined actors.
What operational problems can it create for SaaS teams?
Lower conversion, more support tickets about pending charges and billing fear, and increased exposure to fraud if attackers use your flow for card testing.
What’s a better pattern for expensive AI/GPU/API products?
Layered controls + adaptive friction: bot management and rate limits first, then require a card only for high-cost actions, with strong anti-fraud protections.
View in Twitter X

